Network Monitor
Nearly everyone relies on the Internet and the connection to it. It provides a means to communicate, socialize, and do business. The Internet serves as a place we go to and rely on for just about everything. Among the countless activities we do, it’s a necessary part of our lives. We depend on it being available when needed.
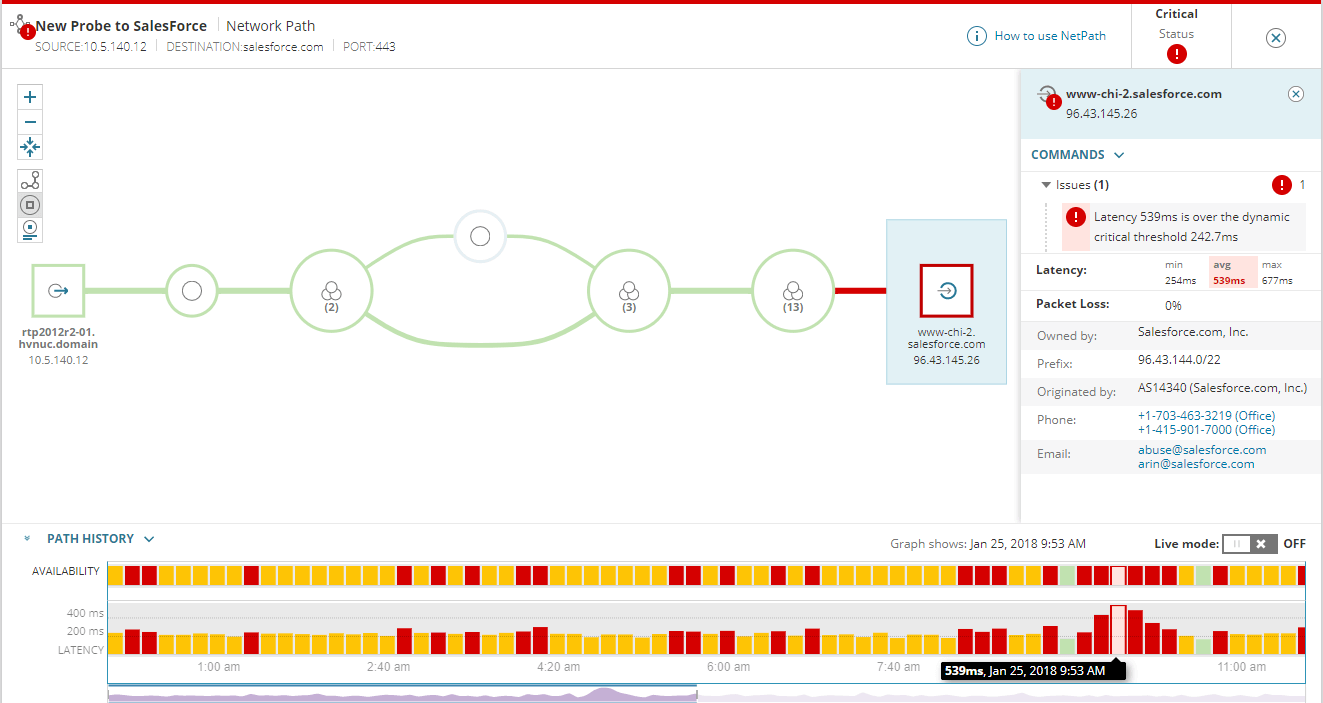
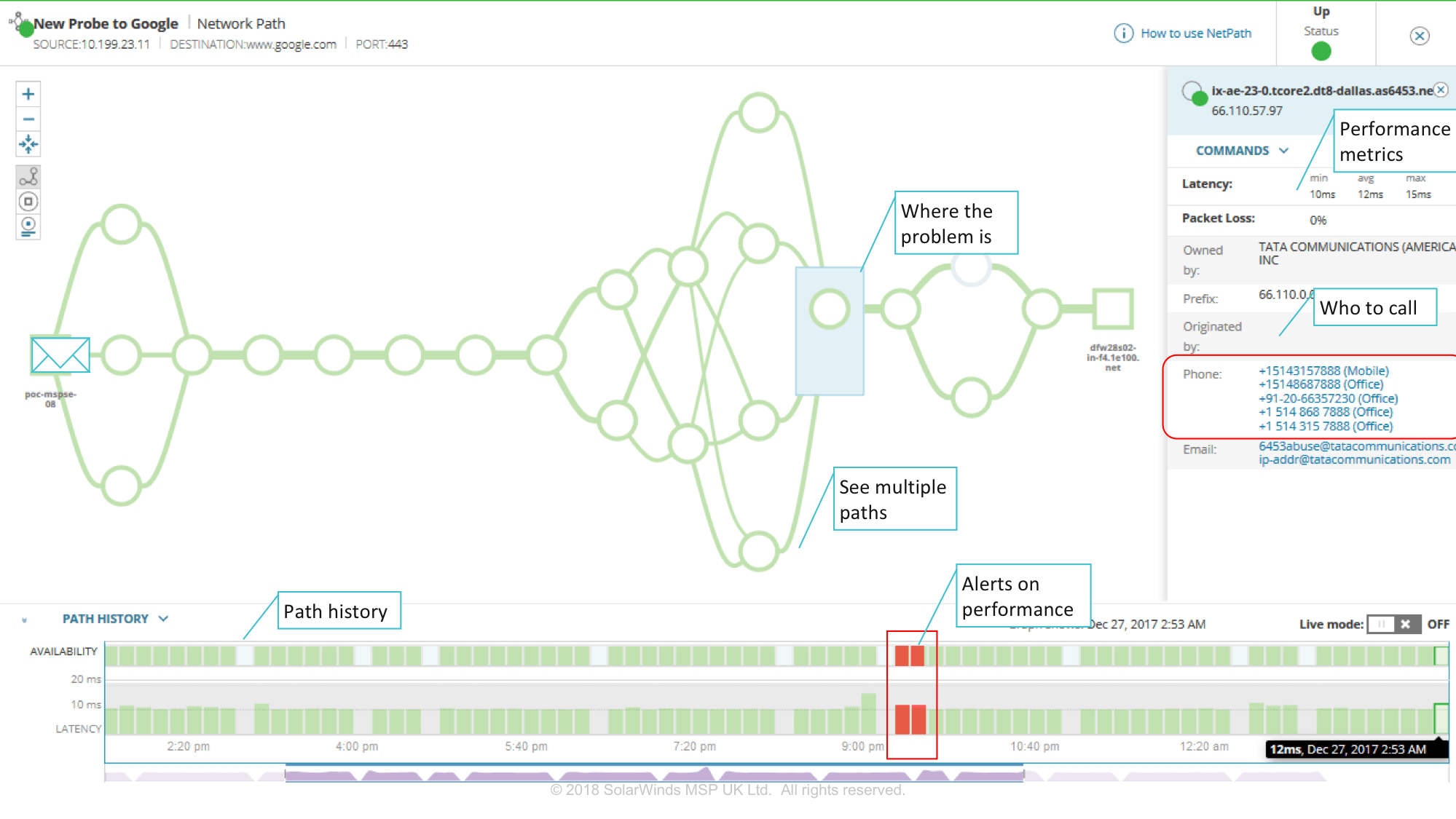
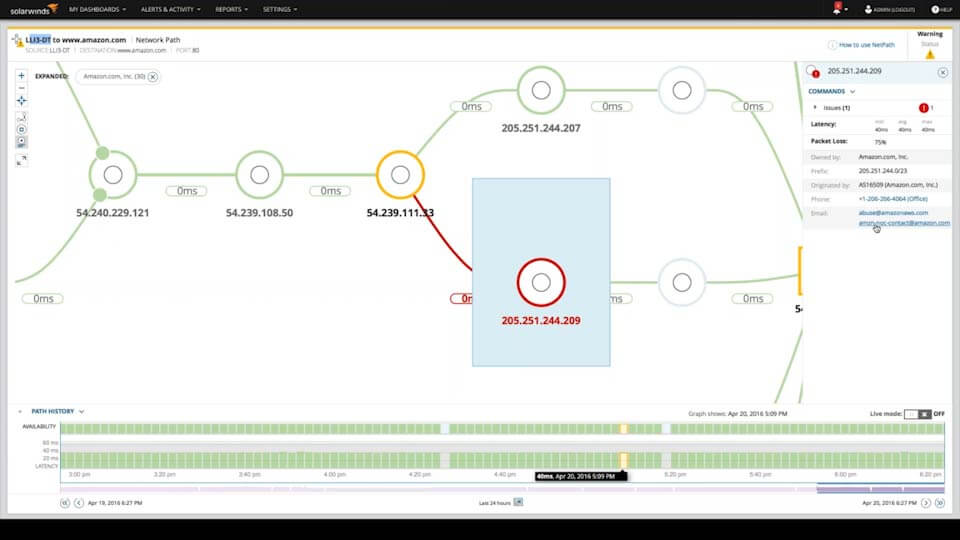
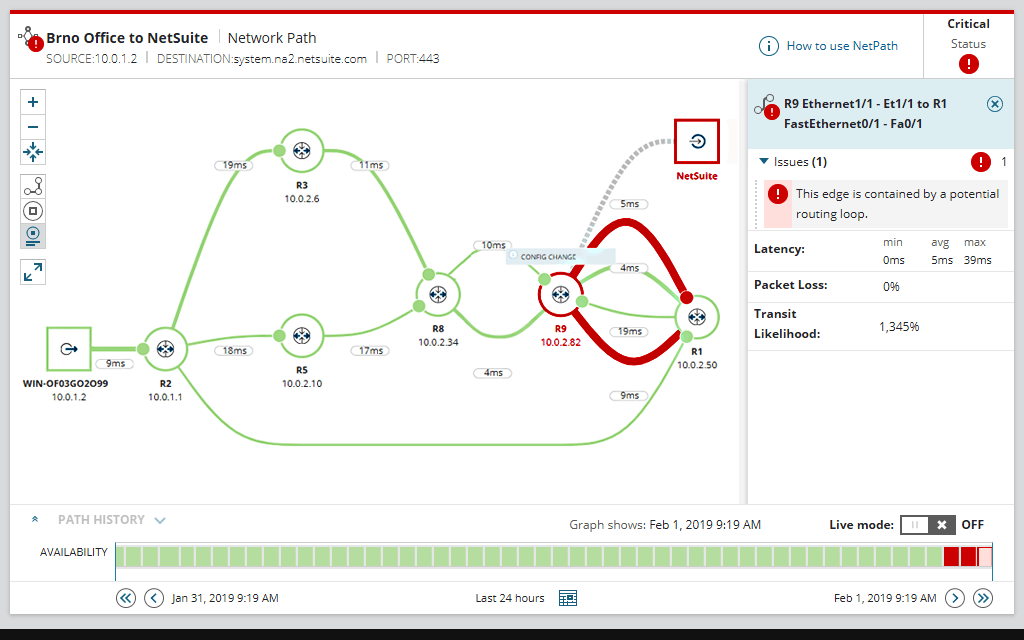
Network Monitor implements a visual history of a connection and its path to its destination. It reveals a wealth of information identifying routes, hops, latency, and issues historically or in real time.
Network Monitor gives you complete control of your Internet. View performance, traffic, and configuration details of devices and applications. It can isolate network slowdowns and determine the person you need to contact to solve them. Understand your provider’s network better than they do with visibility to the entire network path.
Track every hop and view latency historically or in real time. Network Monitor can establish 5-minute intervals for monitoring. It saves all historical data on path performance – saving you time troubleshooting by having an incremental timeline of path history for the last 30 days.
Know about outages immediately. The Network Monitor feature collects performance metrics and details of the network connectivity between the source and destination nodes, thus enabling a visual representation of experienced end-to-end performance capable of identifying thresholds crossed for packet loss and latency.
When your Internet connection drops or your website goes down, it may be necessary to pass on crucial information to administrators. Quickly identify issues and isolate problems.
Russell Kirkpatrick, Founder/CEO
KEY ELEMENTS
Performs checks against SNMP-enabled devices, including routers, switches, firewalls, and printers.
It keeps track of the ever-increasing number and type of devices connected to an office network, and it provides online status
A potentially multi-path map between a Windows node and the specified destination, displaying performance details and supporting information for devices both inside and outside of your network.
Performance metrics and details of the source and destination nodes along with the primary connection.
Deeper insight into networks to isolate the node or connection that is decreasing end-to-end performance.
Enhanced quality of service for end-users.
24×7 monitoring of the network path.
A Path History to check the networks performance over the last 30-days.
Checks are automatically added for each path to alert you to any discovered problems.
Connection Drop
Remote system connectivity is crucial to workplace functionality, reliability, and safety.
1-Node
Do you need to monitor your Internet connection? Establish live connectivity awareness of network nodes along its path to identify issues when they occur.
3-Nodes
Do you need to monitor your Internet or websites? Establish awareness of network paths and nodes. Identify when outages occur and analyze the issue.
10-Nodes
Need more awareness than the average Joe? Dial into multiple network nodes, websites, and servers. Establish an understanding of network paths and nodes.
20-Nodes
Have an extensive network of servers that require monitoring for outages? Establish an understanding and detailed awareness of network paths and nodes.
Package Comparisons
-
Sale!

Website Hosting (WordPress)
$120.00Original price was: $120.00.$50.00Current price is: $50.00. on the 1st of each month -
Sale!

Private Mail (Basic)
$8.00Original price was: $8.00.$6.00Current price is: $6.00. on the 1st of each month -
Sale!

Computer Protection (Fortified)
$50.00Original price was: $50.00.$30.00Current price is: $30.00. on the 1st of each month with a 30-day free trial and a $5.00 sign-up fee -
Sale!

Private Mail (Premium)
$15.00Original price was: $15.00.$12.00Current price is: $12.00. on the 1st of each month